This is part 2, to learn how to setup a lab for WVD see part 1.
The first rule of securing WVD is to block all internet ports to the WVD infrastructure. You should not open TCP 3389 because Windows Virtual Desktop doesn’t require any open ports for users to access the host pool’s VMs. WVD uses Reverse Connect, which reduce the risk involved with having remote desktops brute forced from the internet.
The second rule of securing WVD is to enable MFA. Otherwise, if an attacker knows the email address, brute force is possible (or easier if the attacker obtains the password from a data breach since most users recycle their passwords). The location of the WVD environment is not a secret since most organizations will publish a deterministic TXT record that is always in the format of _msradc.(domain.com), like _msradc.contoso.com.
So security for WVD is similar to how we secure other M365 applications such as Exchange Online, SharePoint Online, Teams, OneDrive for Business, etc.
Identity Best Practices for WVD
1. Implement MFA for WVD.
Prerequisites:
a. Azure AD Premium P1 license is applied to the user accessing WVD
b. The user has previously enrolled into Azure AD MFA. (http://myprofile.microsoft.com)
c. Create a conditional access policy that targets the WVD application
Windows Virtual Desktop (App ID 9cdead84-a844-4324-93f2-b2e6bb768d07)
(If you are using the older WVD Classic (early adopters of WVD) then there is a different application you will select, learn more here.
2. Setting Expectations for the user’s MFA experience. For devices that authenticate with MFA at least once, they receive a token that allows the user to avoid additional (and arguably unnecessary) MFA prompts since they have already proven they are not a hacker. Some organizations still require MFA prompts for every single authentication attempt. The closest to that requirement is to set the CA Session refresh timeout to 1 hour (that is the minimum), which will require multifactor authentication if a connection is launched an hour after the last one. To configure this go to the Conditional Access policy created in step 1 and then select Session, select Sign-in frequency, set the value to the time you want between prompts.
3. Use IP Fencing (sparingly). For example, if the outside vendor that needs to access your WVD environment always connects from a specific static IP address, you could create the conditional access policy to block access to WVD from any IP address other than the permitted IP address ranges. This scales reasonably well even for large organizations since you can have 2,000 IP ranges per named location (and a max of 195 total named locations). This works mostly for businesses because most people’s home ISP will rotate the IP address periodically.
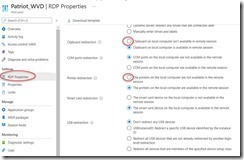
Disable Redirections
To prevent data from being copied outside of the WVD VM you can disable some of the redirections such as Clipboard and local drive access.
You can do this in the GUI or in PowerShell.
To learn how to connect with PowerShell, click here.
For example:
· redirectclipboard:i:0 disables clipboard redirection.
· usbdevicestoredirect:s: disables USB device redirection.
· devicestoredirect:s: disables redirection of plug and play devices.
· drivestoredirect:s: disables local drive redirection.
· redirectprinters:i:0 disables printer redirection.
To learn more about customizing RDP properties for a host pool using PowerShell or the Azure portal, check out RDP properties. For the full list of supported RDP properties, see Supported RDP file settings.
Block Screen Capture
The WVD client for Windows 10 has a unique feature that can prevent the host machine from taking screen shots of the applications running inside the WVD. This is done by adding a registry key to the WVD host computer in azure that is hosting the virtual machines. Since only the Windows client supports this, you could create a conditional access policy that prevents other operating systems from connecting to WVD (block mac, mobile and browser clients).
reg add “HKLM\SOFTWARE\Policies\Microsoft\Windows NT\Terminal Services” /v fEnableScreenCaptureProtection /t REG_DWORD /d 1
Learn more here.
RemoteApps vs Full Desktop
Publish RemoteApps rather than the full desktop. If you publish applications instead of the desktop then you don’t need to worry as much about data exfiltration. If you must publish a full desktop then you may want to look into Endpoint DLP for Windows 10 (requires M365 E5 license, Microsoft 365 E5 compliance, or Microsoft 365 E5 information protection and governance). This is likely to work on the WVD Dedicated but may not the WVD multi-session pooled configuration (I’ll have to test that).
Securing Azure AD Domain Services
In many WVD environments, they will be connecting to Azure AD Domain Services. Therefore, securing Azure AD Domain Services is important too.
By default, Azure Active Directory Domain Services (Azure AD DS) enables the use of ciphers such as NTLM v1 and TLS v1. These ciphers may be required for some legacy applications, but are considered weak and can be disabled if you don’t need them. If you have on-premises hybrid connectivity using Azure AD Connect, you can also disable the synchronization of NTLM password hashes.
To learn how to disable NTLM v1 and TLS v1 ciphers and disable NTLM password hash synchronization see Secure Azure AD Domain Services | Microsoft Docs
Azure Defender
For more tips we recommend the Microsoft Documentation ‘Security Best Practices for WVD’ here. For example, enable AppLocker and hide the Windows Explorer and local and remote drive mappings. Set a screen saver timeout, and disconnect idle sessions. Enable antivirus, EDR, and 3rd party vulnerability scanning and patch management. A lot of this is bundled by onboarding the hosts into Azure Defender (formerly known as Azure Security Center Standard). Pricing starts at $14.60 per server per month, see more pricing details here.
Stay Informed
To keep up to date with the latest announcements and improvements to Windows Virtual Desktop, check the release notes here once a month. I’m eagerly looking forward to support for Azure AD Join, so that WVD VM’s don’t have to join traditional domain controllers or AAD Domain Services.
[Update 5/26/2021] – Support for ADFS is now in PUBLIC PREVIEW: Announcing public preview of SSO using AD FS – Microsoft Tech Community